Network Architecture
Cybersecurity Architecture for Maritime Vessels: Technical Overview
Concept Overview
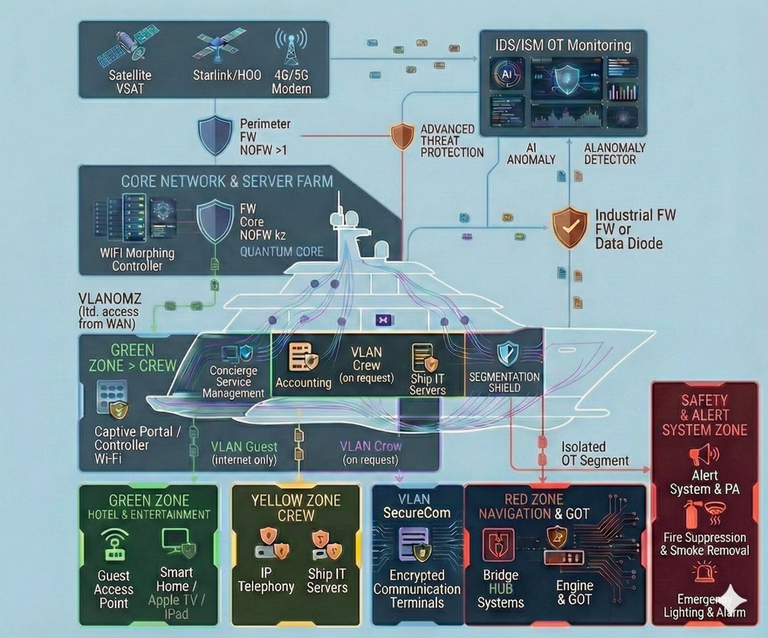
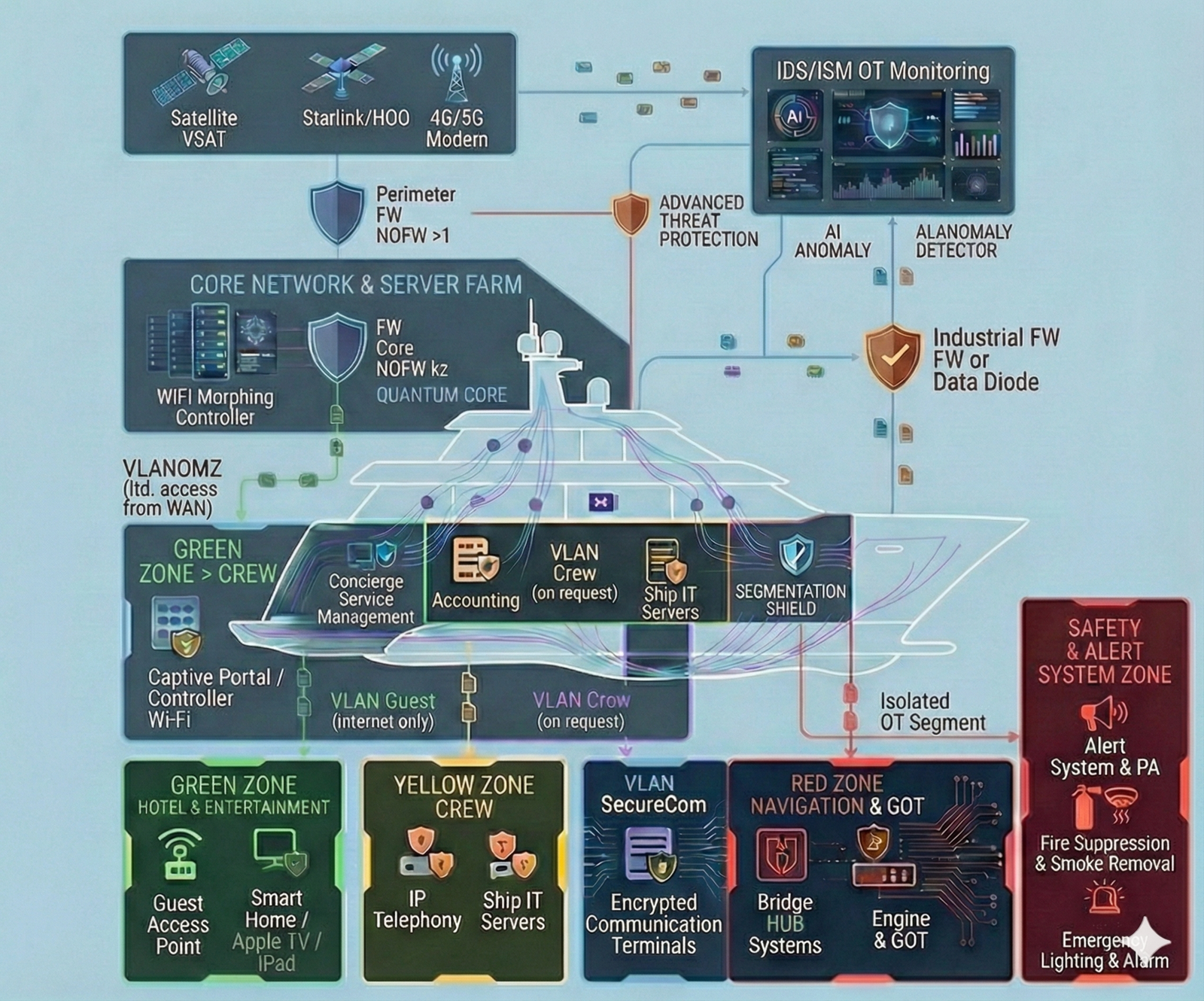
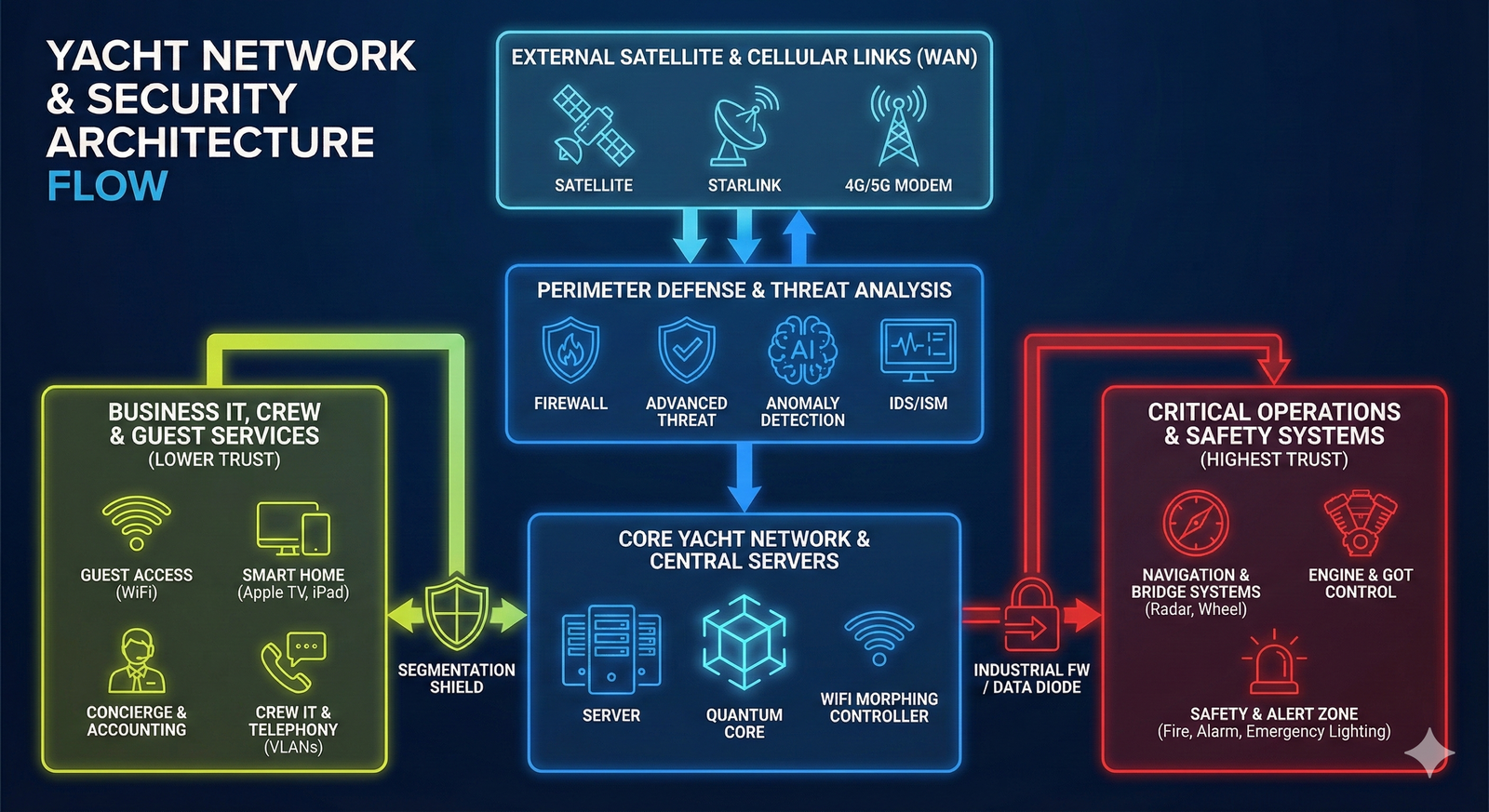
The diagram presents a cybersecurity architecture for maritime vessels, built on the principles of Defense-in-Depth and Zero Trust. The solution is designed to securely converge shipboard IT services (crew, passenger/guest services, shore office, vendors/contractors) with mission-critical operational technology (OT/GOT)—navigation, communications, power/energy, machinery control and automation.
In today’s operating environment, onboard cybersecurity is not an “optional add-on” and it is not only about protecting data. It is a necessary safety measure for safe navigation and ship operations, supporting the integrity of command and control, the resilience of onboard systems, and the continuity of vessel operations—from preventing unauthorised access and disruptions to reducing the risk of safety incidents driven by digital interference with ship systems.
The approach is applicable across a wide range of maritime assets: commercial vessels, passenger ships and ferries, tankers, container ships, OSV/offshore, as well as large yachts. Below is a detailed description of the protection layers and key components.
1. External Perimeter & Multi-Bearers Connectivity
The first line of defence, providing flexible and secure vessel connectivity to global networks.
- Connectivity Sources: Aggregation of links to maintain communications worldwide:
- Satellite VSAT: Traditional, reliable connectivity via GEO satellites.
- Starlink/LEO: High-throughput, low-latency connectivity via low-earth-orbit constellations.
- 4G/5G Modem: Cellular connectivity in coastal areas and ports.
- Perimeter FW (Firewall) NOFW >1: A high-performance border security gateway in a high-availability setup (>1). Performs primary traffic filtering at the “ship-to-shore” boundary and terminates VPN tunnels.
- Advanced Threat Defense: Cloud or on-prem “sandbox” service to analyse suspicious files for zero-day threats before they reach the network.
2. Secured Network Core & Services (Core Network & Server Farm)
The central node for data processing and policy enforcement.
- Core Firewall (Core FW) NOFW k2 "Quantum Core": The heart of the security system. A resilient cluster of internal firewalls (k2 configuration). The “Quantum Core” processing layer delivers very high DPI performance and is positioned for future adoption of post-quantum cryptography.
- Wi-Fi Morphing Controller: An advanced wireless management system using Moving Target Defense—dynamically changing network parameters (BSSID, SSID, keys) to reduce discoverability and mitigate “evil twin” style attacks.
- VLANOMZ: A dedicated Management Zone for infrastructure servers with strictly restricted access from WAN and user segments.
3. Active Monitoring & AI Analytics (Overlay Security)
An overlay layer for proactive, real-time threat detection without interfering with operations.
- IDS/ISM OT Monitoring: An intrusion detection capability adapted to maritime operations (ISM - International Safety Management).
- OT Cyber Sensor: Passive sensors connected to OT networks, analysing vessel-specific protocols and telemetry for anomalous commands.
- AI Anomaly Detection: AI-driven analytics that identify hidden threats by detecting deviations from normal network and system behaviour beyond signature-based methods.
4. Strategic Segmentation (Segmentation Shield)
The “Segmentation Shield” visualises strict separation of the network into isolated zones with different trust levels.
- GREEN ZONE:
- Passenger/Guest Services & Entertainment: An isolated segment for passengers/guests (smart services, media, personal devices) with Internet-only access via Captive Portal / Wi-Fi Controller.
- Crew (CREW): Segments for administrative tasks (back office, concierge/support services) and separate personal access for crew (VLAN Crew on request/policy).
- YELLOW ZONE (CREW): Operational environment for service IT servers and IP telephony.
- VLAN SecureCom: A dedicated segment for encrypted terminals used for confidential communications.
5. Protection of Critical Ship Systems (RED ZONE)
The “Red Zone” is a Zero-Trust segment housing systems essential for vessel safety and operability.
- Navigation & GOT: Includes bridge navigation systems (Bridge NAV Systems), engine control and other operational technologies (Engine & GOT).
- Industrial FW or Data Diode: A critical barrier enforcing one-way data flow. It allows telemetry to move out of the OT segment into monitoring systems, while physically blocking inbound connections or attacks into the Red Zone.
Glossary: Terms & Abbreviations
To ensure unambiguous understanding of the technologies used, the following terms and abbreviations are provided:
| Term / Abbreviation | Description |
|---|---|
| AI Anomaly Detection | AI Anomaly Detection. An AI/ML-based system that detects threats not via known malware signatures but via deviations from normal network and user/system behaviour. |
| Captive Portal | An authentication web page presented to a user before access is granted to a public/guest Wi-Fi network (e.g., passenger/guest zone). |
| Data Diode | Data Diode. A hardware cybersecurity device that physically enforces one-way data transfer (out of a protected segment), eliminating inbound attacks. |
| GOT | Generic Operational Technology. An umbrella term for shipboard control and automation systems (propulsion, power, HVAC, machinery, etc.) critical to safe operations. |
| IDS/ISM | Intrusion Detection System / International Safety Management. Intrusion detection aligned with the vessel’s safety management processes. |
| LEO | Low Earth Orbit. Satellite systems such as Starlink providing high bandwidth and low latency. |
| NOFW (>1 / k2) | Internal designation for high-availability / high-performance Network Firewall cluster configurations. |
| OT Cyber Sensor | OT Cyber Sensor. A specialised device for passive monitoring of OT networks without impacting control processes. |
| Quantum Core | Quantum Core. A marketing designation for the high-performance processing module of the Core FW, designed for large-scale traffic inspection and future cryptographic readiness. |
| Segmentation Shield | Segmentation Shield. A visual representation of deep logical isolation between network zones to prevent lateral movement and threat propagation. |
| VLANOMZ | VLAN Operations Management Zone. An isolated virtual network for infrastructure management with strictly restricted access from WAN and user segments. |
| VSAT | Very Small Aperture Terminal. Traditional satellite connectivity via GEO satellites for global coverage. |
| Wi-Fi Morphing | Wi-Fi Morphing. A Moving Target Defense approach for wireless networks—continuously changing parameters (BSSID, keys, etc.) to hinder reconnaissance and Wi-Fi attacks. |
| FW | Firewall. |
Functional Block Diagram of Ship Systems Logic
1. External Layer: Connectivity and Data Ingress (WAN)
- Components: VSAT, Starlink/LEO, 4G/5G modems.
- Function: Vessel ↔ shore communication and Internet access.
- Flow: Primary entry/exit point for all data traffic.
2. Security Perimeter and Access Control
- Components: Perimeter Firewall, Advanced Threat Protection (ATP).
- Function: Traffic filtering, blocking external attacks and unauthorized access.
- Components: Operations Management Zone (OMZ).
- Function: Regulated contractor and administrator access.
- Feature: Isolated from guest and general crew traffic.
3. Core Layer: Network Intelligence
- Components: Core Firewall, network backbone, Wi-Fi controller.
- Function: Routing, resource allocation and policy enforcement.
- Components: AI anomaly detection, cyber sensors, monitoring dashboards.
- Function: Analysis of logs and events from IT and isolated OT segments (via Data Diode).
4. Internal Segmentation: User and Service Zones
DIRECTION A: Passengers / Guests
- Systems: Wi-Fi access, multimedia, user devices.
- Status: Fully isolated from control systems. Internet-only access.
DIRECTION B: Crew and Administration
- Administrative processes, documentation, logistics.
- IP telephony, shared crew servers.
- Encrypted terminals for confidential communication.
5. Critical Infrastructure: OT and Safety Systems (Red Zone)
Principle: One-way data flow — monitoring allowed, inbound access physically blocked.
- Systems: Bridge systems, ECDIS, engine room, GOT.
- Status: Fully isolated.
- Systems: PA, fire detection and suppression, emergency lighting.
- Function: Autonomous safety and emergency response support.