VASSTA — Cybersecurity for yachts and maritime assets
CYBERSECURITY
safeguarding business interests
The maritime digital environment connects vessels, infrastructure and offshore into one system. Large yachts are its most technologically advanced segment, demanding cybersecurity that matches their engineering excellence.
While traditional IT support focuses on routine technical tasks, we safeguard your maritime operations from cyber risks that can cause financial, reputational, navigational, and physical safety impacts
Navigation Disruption (OT)
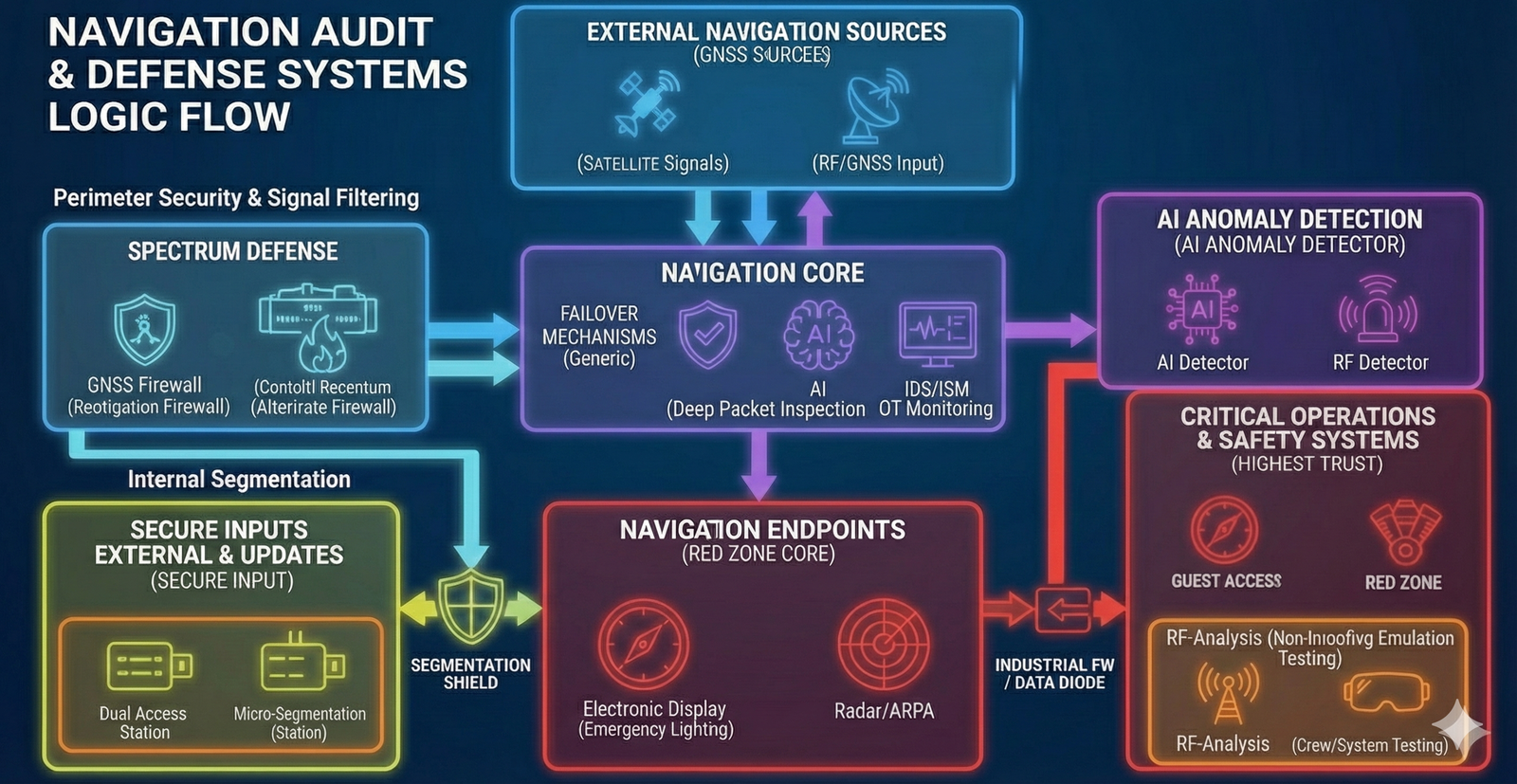
Any interference with a vessel’s navigation systems or its key control systems can distort critical data and lead to incorrect situational awareness. If communication channels with shore offices or service providers are compromised, the risk increases — decisions may be made based on inaccurate or manipulated information. For a vessel, this directly affects navigational safety and operational stability. For ports and offshore infrastructure, it may result in operational disruptions and logistical delays. That is why cybersecurity must protect not isolated systems, but the entire connected environment — Vessel ↔ Shore ↔ Offshore — with onboard safety remaining the priority.
Corporate Espionage
Confidential conversations of the owner and key personnel may be intercepted if network infrastructure is compromised or communication channels — including VoIP and messaging platforms — are insufficiently protected. This may allow attackers to obtain commercially sensitive information, details of negotiations, operational plans or financial matters. For a vessel, this creates strategic and reputational risks. For infrastructure operators, it may affect competitive position and business stability. That is why communication security must be treated with the same priority as navigational and technical system protection.
Cyber Incident Unpreparedness
Without a clearly defined incident response and recovery plan, crew and personnel may act inconsistently or with delays during a cyber incident. If satellite communication or onboard networks are disrupted, this may result in loss of connectivity, operational downtime and extended recovery time. For a vessel, this creates operational instability and prolonged disruption. For ports and offshore infrastructure, it may lead to process interruptions and financial impact. That is why defined response procedures, clear role allocation and recovery readiness are essential elements of modern cyber resilience.
Critical Infrastructure Protection Standards
With expertise built since 2004, we deliver reliability trusted in high-risk and highly confidential environments
Privacy Protection
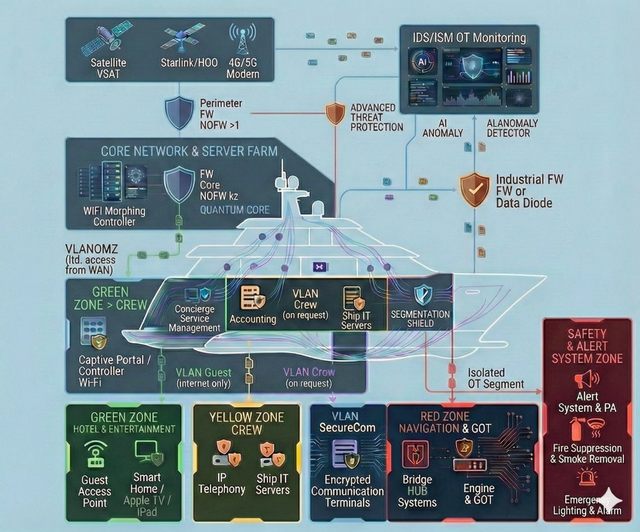
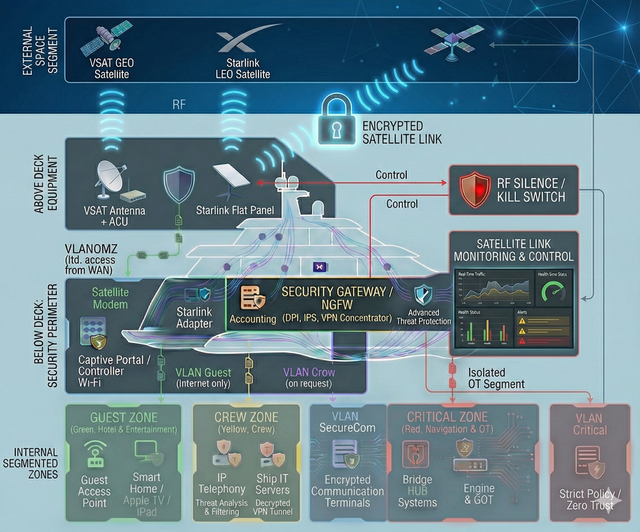
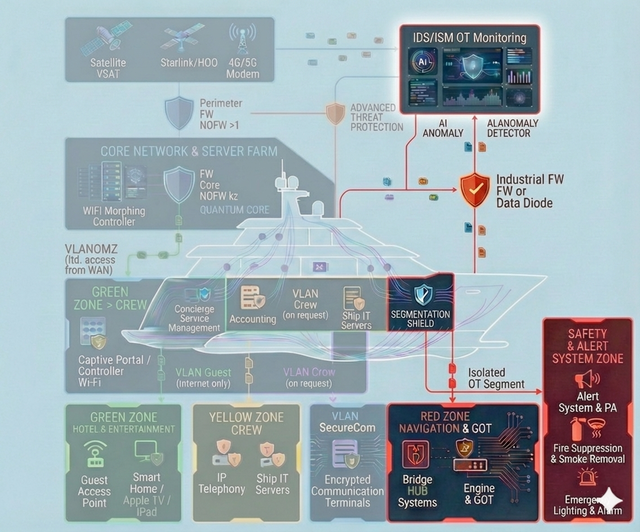
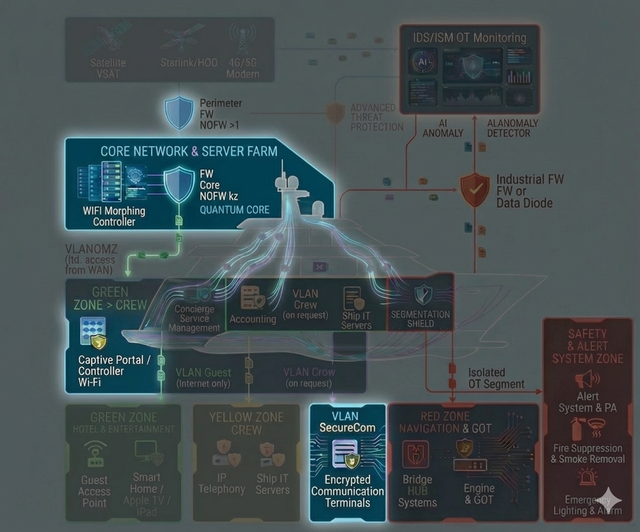
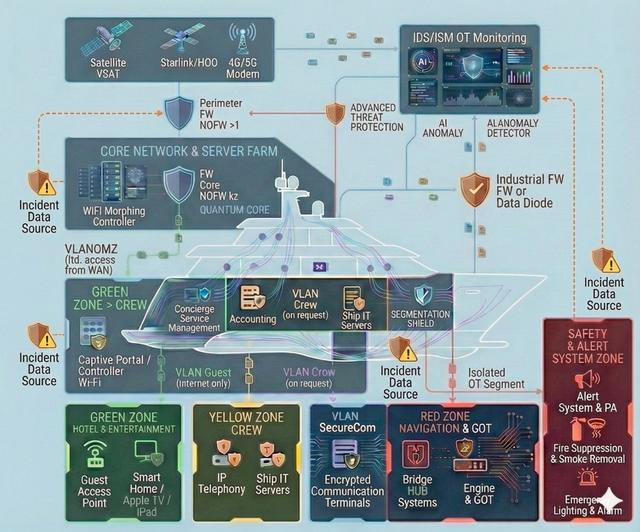
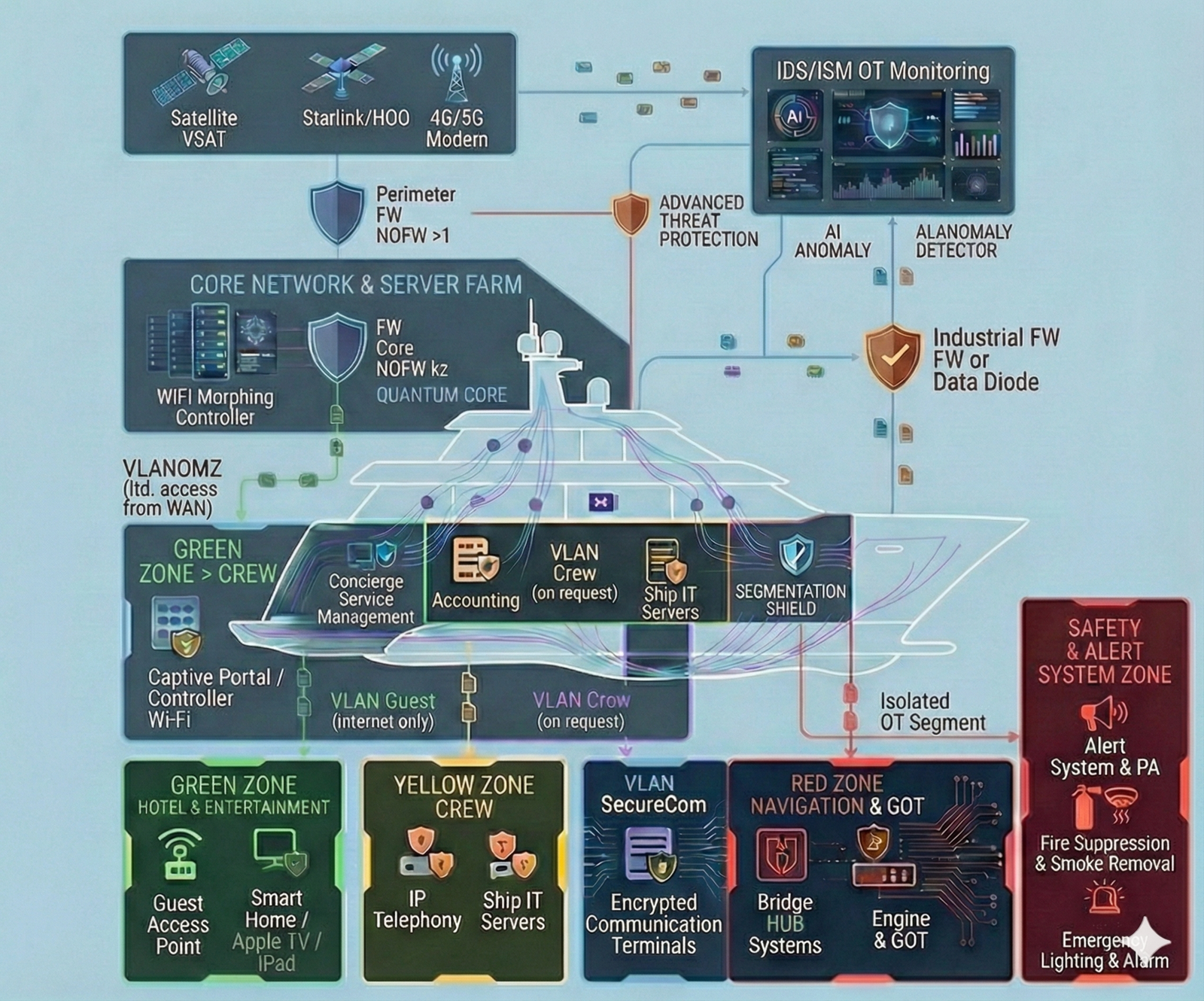
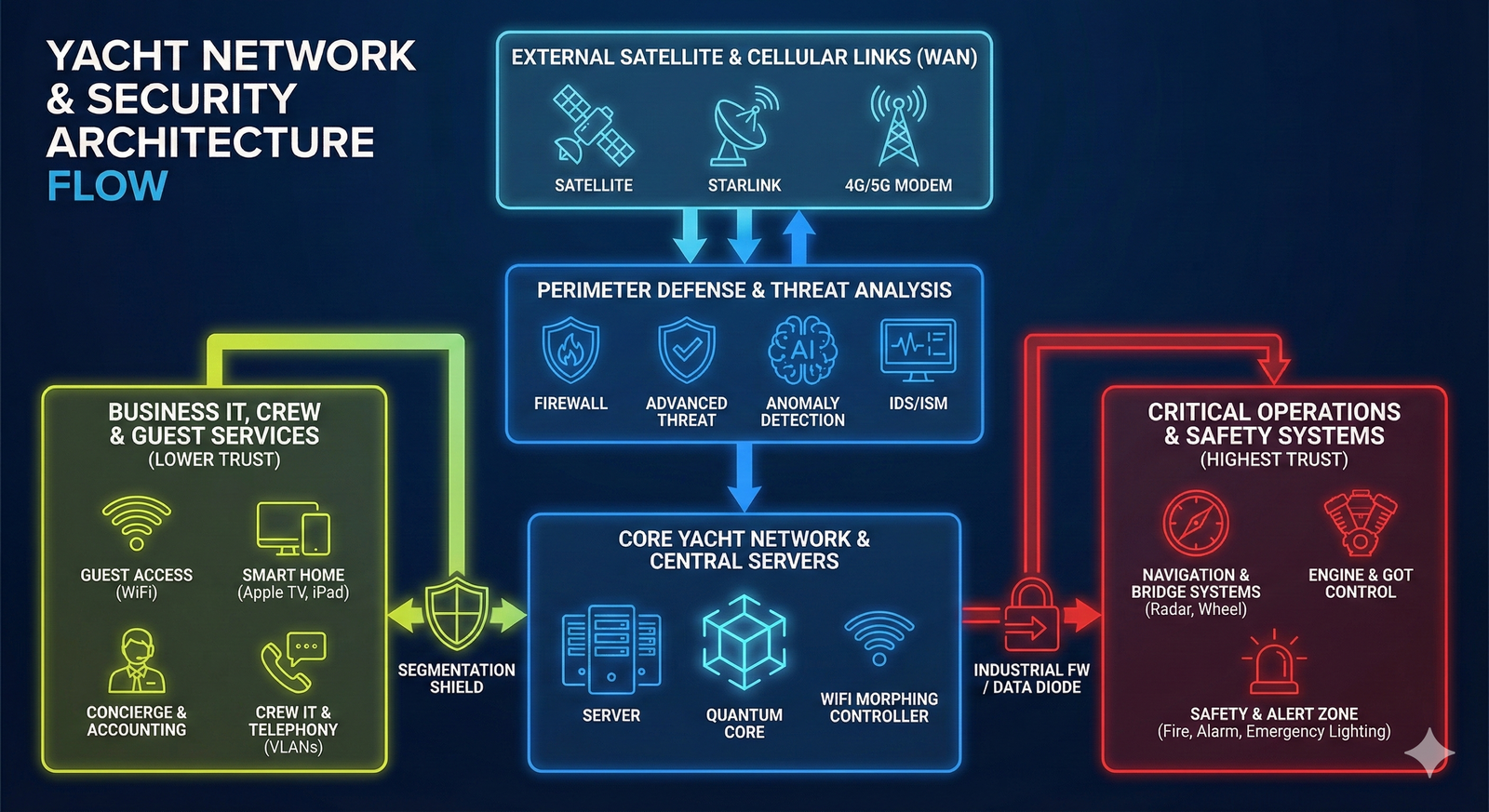
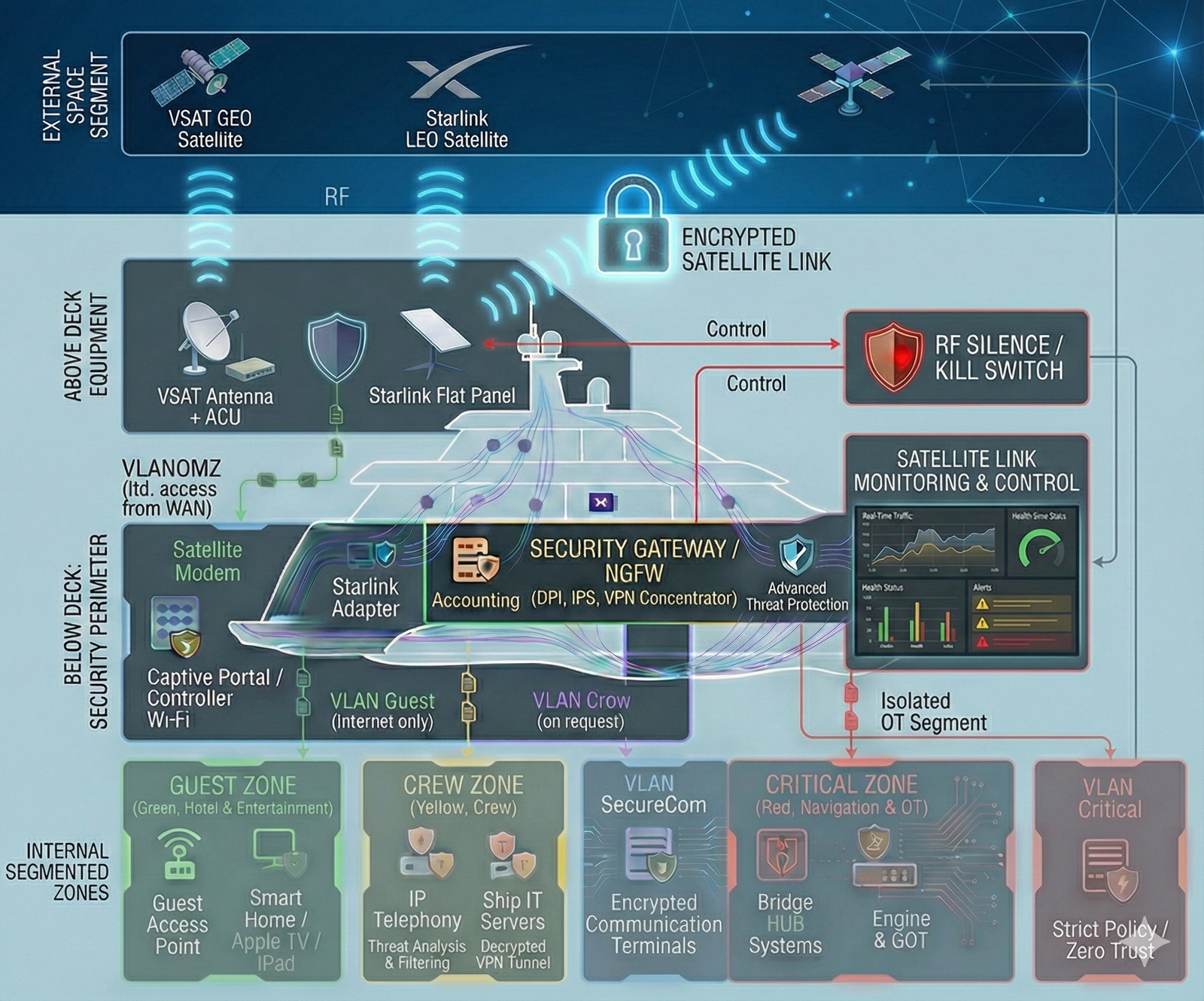
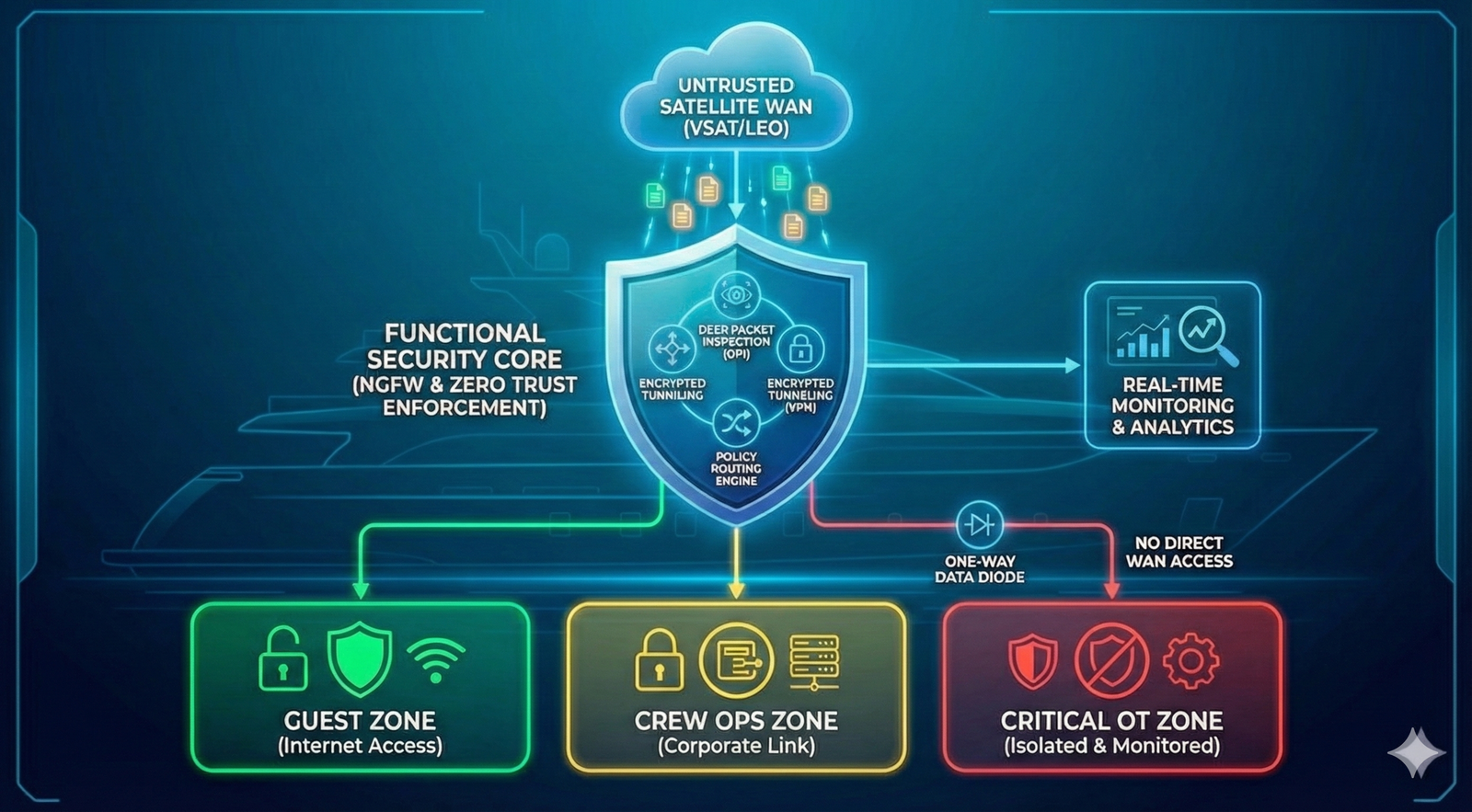
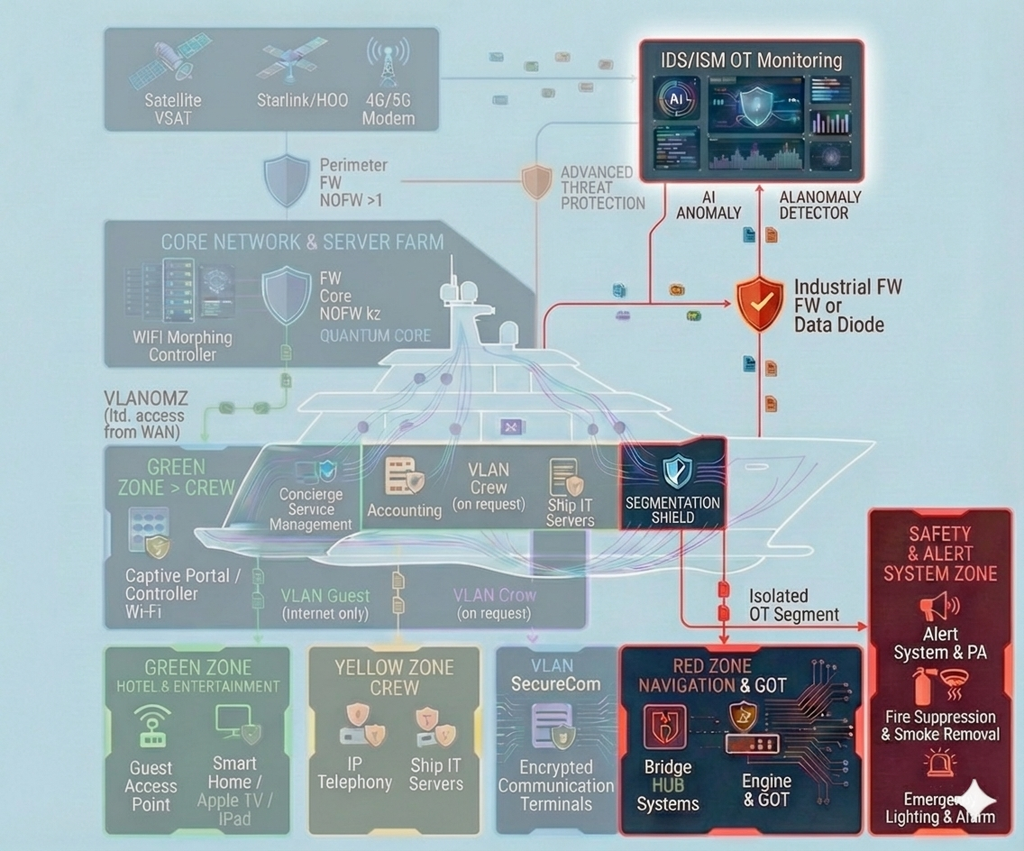
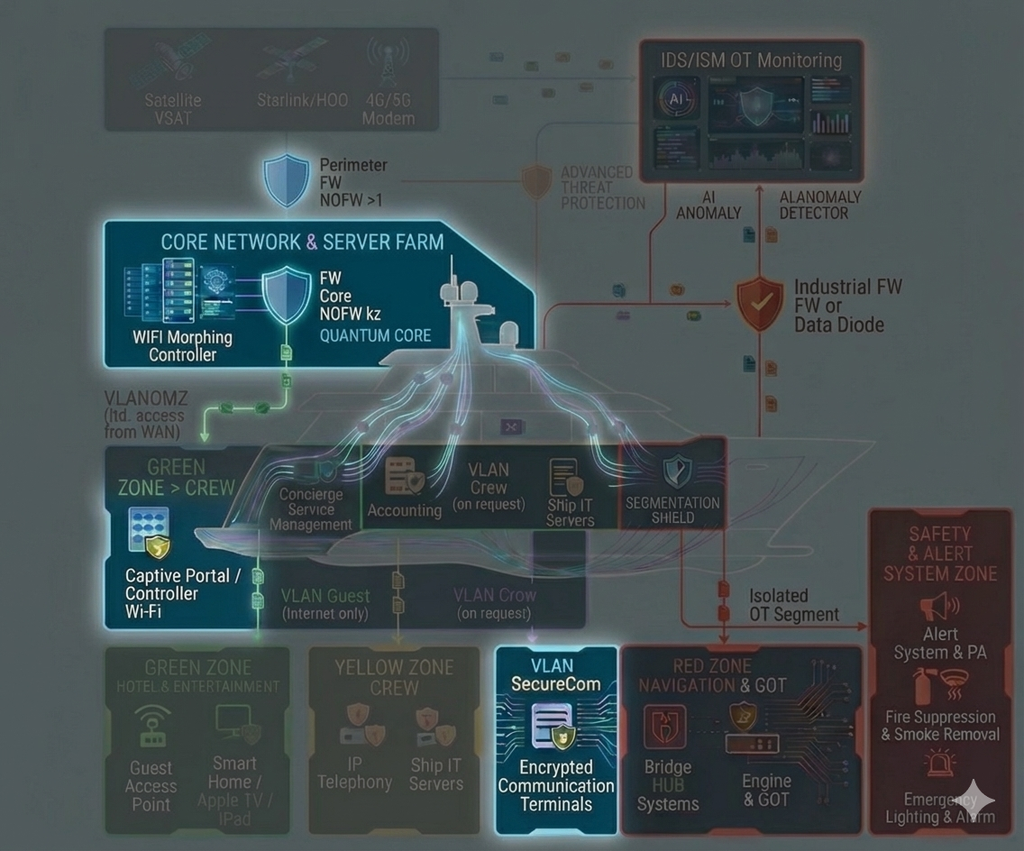
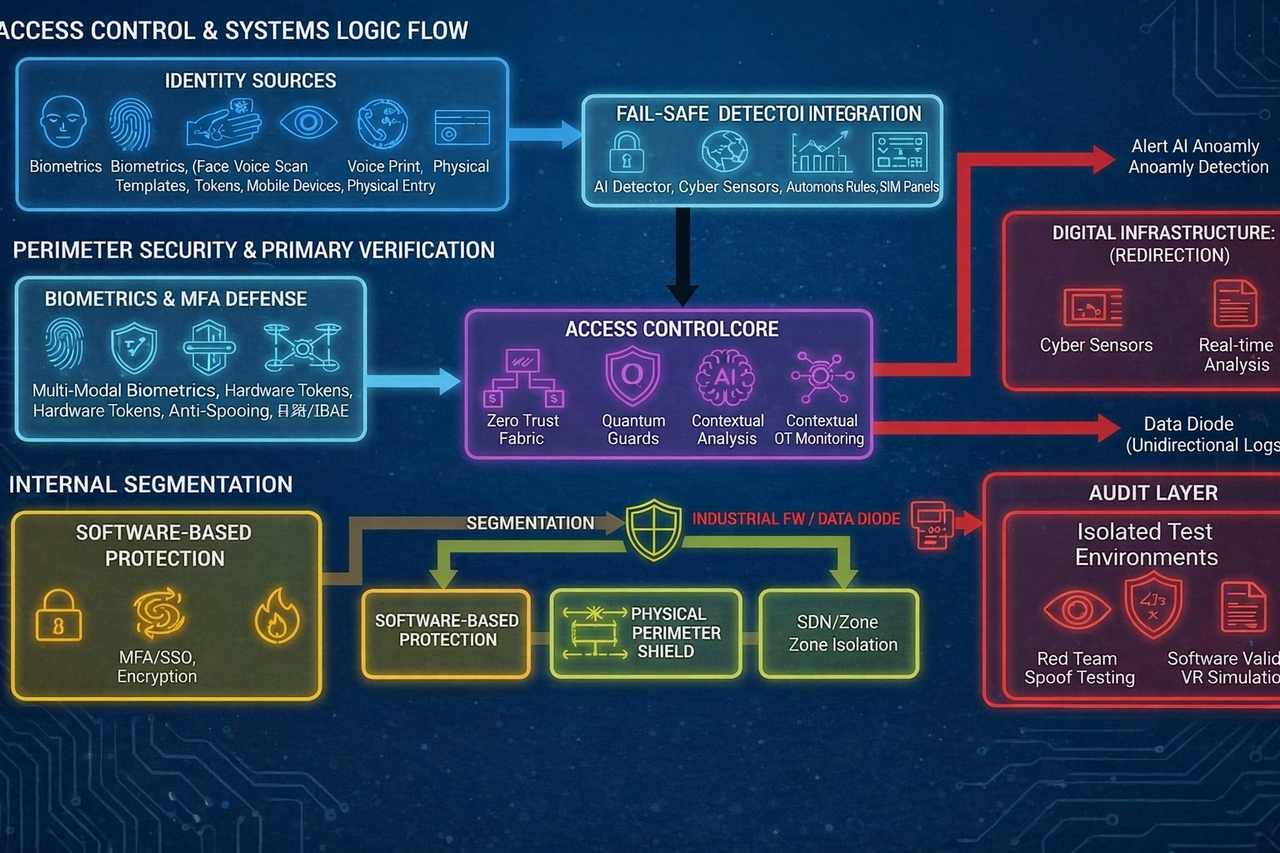
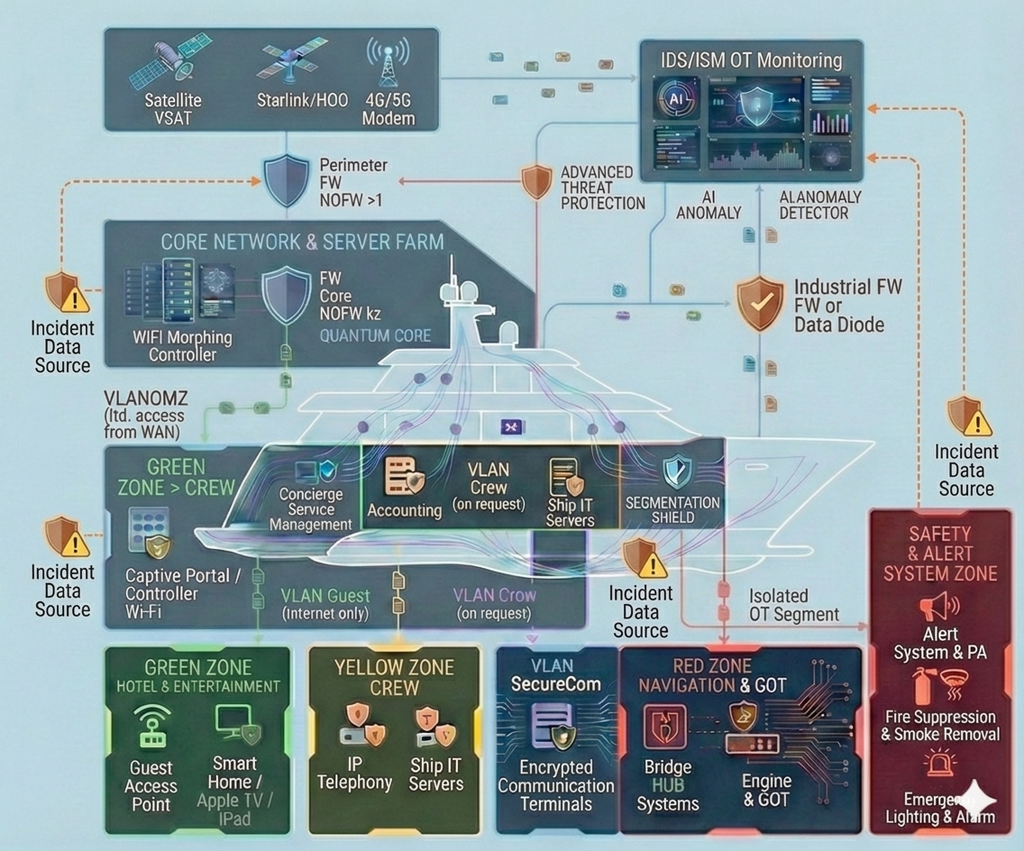
We establish segmented “Clean Zones” — isolated, access-controlled digital environments for navigation systems, critical services and confidential communications. This approach is applied both onboard vessels (including privacy-sensitive yachts) and across connected shore and offshore segments where sensitive data and operational processes require enhanced protection. The architecture follows strict cybersecurity practices, minimizing the risk of data leakage, unauthorized access and impact on critical maritime systems.
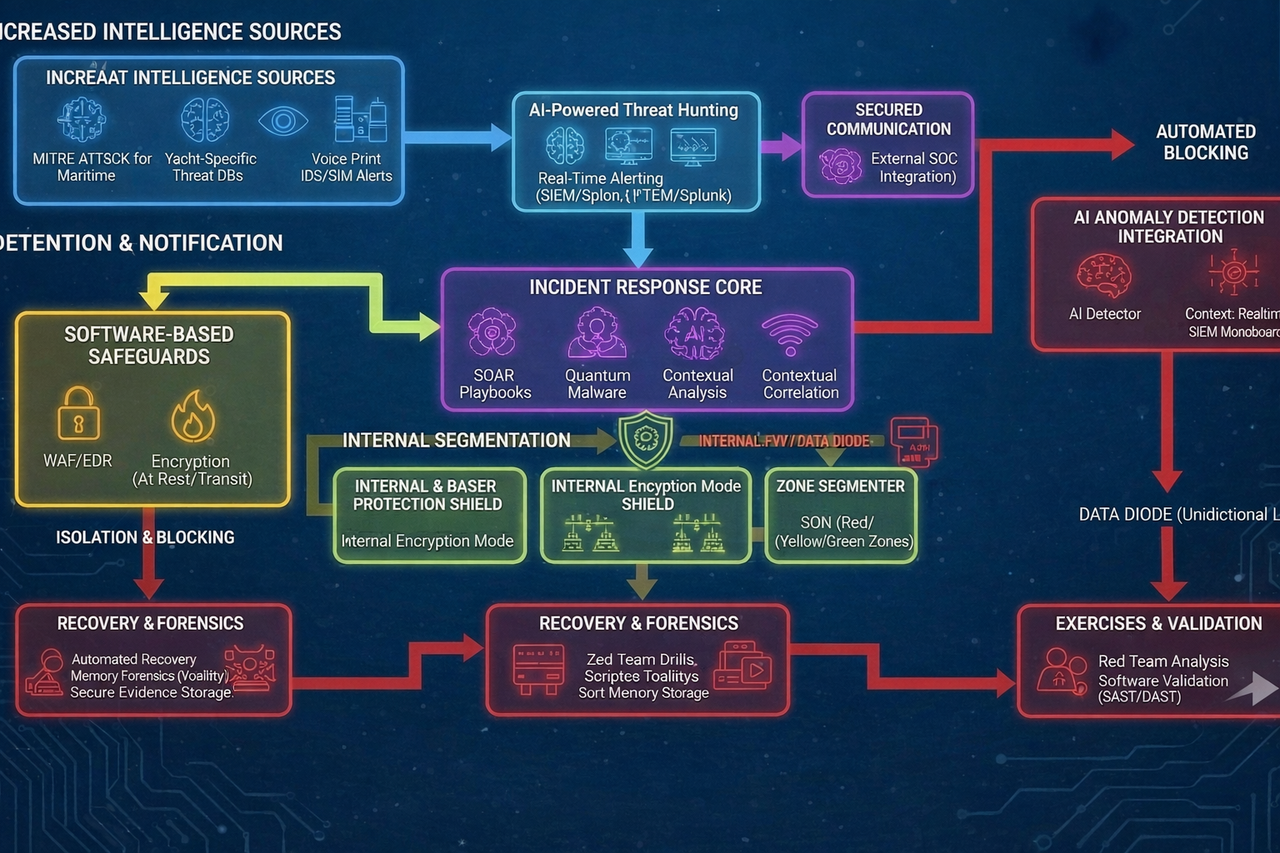
Incident Response (IR)
Our cybersecurity architecture provides continuous monitoring and early detection of incidents across vessels as well as connected shore and offshore segments. It enables rapid containment and controlled mitigation while minimizing impact on critical operations. As part of the process, digital forensics analysis is performed to determine the origin and attack vector, preserve evidentiary data and ensure structured system recovery within the shortest possible timeframe — with onboard operational safety as the priority.
Practical Compliance
We prepare maritime vessels for compliance with IMO cyber risk management requirements (MSC.428(98)) and IACS UR E26/E27 through demonstrable implementation of technical and organizational controls. Our approach prioritizes structured risk assessment, protection of safety-critical systems and defined response procedures — focusing on real operational resilience rather than formal documentation closure. The methodology extends to port and offshore infrastructure within the unified “Vessel ↔ Shore ↔ Offshore” environment. Large yachts are treated as a distinct profile due to their higher IT/OT density and privacy requirements, requiring deeper segregation and tailored control measures.
Technical Expertise
Services
Special Offer
We document your vessel’s IT/OT infrastructure — as the most complex and security-demanding element of the maritime digital environment — together with its associated shore and offshore interfaces, in their current (“as-is”) state within a Digital Technical Passport for IT/OT systems and cybersecurity. All work is performed without operational disruption, without downtime and without taking systems out of service. We consolidate and structure asset inventories both onboard and across related infrastructure segments, configurations and software versions, technical documentation, responsibility boundaries between vessel, shore and third-party contractors, as well as baseline security controls and operational procedures. The result is a continuously updated, auditable and interconnected single source of truth for the crew, the shipowner and the shore organization, with the vessel maintained as the central and most critical element of the maritime digital ecosystem. Delivery format: a dedicated Private SaaS platform with secure VPN access, providing a unified control and documentation environment for the shipowner, the Master, technical management and relevant infrastructure operators.
VIP Privacy Shield
We implement a structured protection framework for service devices used by crew, shore and offshore personnel — smartphones, laptops and tablets — including hardened configurations, integrity control and secure access to onboard, infrastructure and corporate services. The objective is to reduce risks of data leakage, account compromise and operational disruption across vessels and related facilities. The approach can extend to devices used by owners and executive management depending on the vessel type and operational profile. Secure communication channels are established for confidential discussions, alongside measures to detect and mitigate digital surveillance and unauthorized access. The solution applies to commercial fleets, infrastructure operators and large yachts, where enhanced privacy and executive communication security requirements are addressed.
Navigation & OT-Security
We implement strict segmentation and isolation of safety-critical systems, establishing protected zones for navigation (including ECDIS) and propulsion control to prevent incidents in guest, office or service networks from affecting vessel safety. Additional measures address navigation data integrity and GPS spoofing, alongside centralized control of remote access to critical systems through a single entry point, activity logging, multi-factor authentication and least-privilege principles. The approach extends to connected shore and offshore environments where similar segregation of operational networks is required. It applies to commercial fleets and infrastructure operators as well as large yachts, where contractor isolation and satellite connectivity risks demand enhanced protection.
24/7 Monitoring & Response
We provide 24/7 monitoring of security events and critical system status across vessels as well as connected shore and offshore environments. This enables early detection of incidents, rapid containment and minimized operational impact. As part of the response process, digital forensics is conducted to determine the origin and attack vector, preserve evidentiary data and ensure controlled system recovery within the shortest possible timeframe — prioritizing onboard operational safety.
Pre-Compliance & Crew Training
We prepare maritime vessels for IACS/IMO inspections by establishing practical cyber risk management readiness, including policies, defined roles, procedures and technical safeguards. Crew training for cyber incident response and phishing awareness is provided, and cybersecurity development is supported throughout the vessel’s lifecycle. The methodology extends to connected shore and offshore environments where comparable risk governance and documented preparedness are required. For large yachts, additional emphasis is placed on privacy and external integration control: contractor and integrator oversight during construction, refit and maintenance, secure delivery requirements, access management and compliance verification.
How to Start
Confidential Initiation & NDA
Contact us to outline your objectives. We ensure complete anonymity, sign a Non-Disclosure Agreement (NDA), and gather initial data. Your privacy is secured from the very first interaction.
Inventory, Audit & Gap Analysis
We conduct a comprehensive digital inventory of your IT/OT infrastructure and assess the crew’s organizational procedures. This stage goes beyond simple checks; we map all assets, identify gaps in IACS/IMO compliance, and pinpoint vulnerabilities to build the foundation for your security documentation.
Electronic Passport & Remediation Roadmap
Based on the audit, we generate the vessel’s Electronic Technical Passport for Information Security Systems. You receive more than a report; you get a structured asset document and a prioritized Roadmap for eliminating vulnerabilities, optimized for both security and budget efficiency.
Contact Us
Ready to discuss cybersecurity for your vessels? Message us to schedule a confidential consultation
Contact Initiation
To maintain confidentiality, we recommend requesting initial consultations exclusively in writing. This ensures accuracy of technical details and creates a secure audit trail for your request.
Email: info@zs-info.ru
— for formal enquiries and document submission.
Telegram: https://t.me/CyberSafeHQ
— a secure channel for prompt text communication.
Address: ул.Свободы 1, офис 211, г. Новороссийск, Краснодарский край, 353900; +7 (861) 765-51-61 (available for on-site support worldwide).